Communications and customer experience teams are not short on new ideas, new platforms, or new…
Examine Your Security Maturity
All too many companies assume the security of their systems and data are adequate until they’re hit with an attack, and by then, it’s too late. The results can be devastating. According to the National Cyber Security Alliance, 60% of small and medium businesses that are hacked go out of business after six months. To monitor, detect, and respond to cyber security attacks, book a meeting with us to discuss your situation.
“But We Have a Firewall!”
Don’t make the mistake of thinking that a firewall is a comprehensive security solution. In fact, it’s only part of one. It examines data coming into and out of your network and provides
extensive filtering. This is powerful, but it’s only one link in the chain.
Especially when protecting your high-value business data, any approach to data and network security that is NOT comprehensive will lead to calamity. Those who simply install a firewall anddeclare themselves secure often find themselves proven wrong.
Where Does Security Fit In?
Every part of your network requires specific security measures for your approach to be complete. Technology experts refer to the parts of your network as “layers,” and there are seven: application, presentation, session, transport, network, data link and physical. Data travels through these layers, and each one has its own protocols and other communication standards that govern its efficient operation.
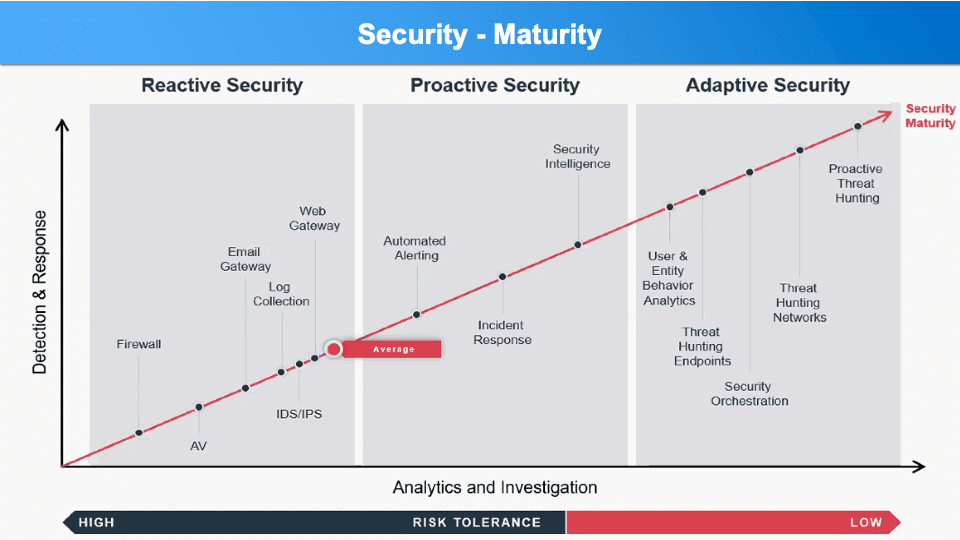
Your Security Maturity
REACTIVE SECURITY
Everybody needs to start their security journey somewhere, and most people start securing their systems by putting up a firewall and some anti-malware, anti-virus, maybe even anti-spam protection.
The purpose of a firewall is to enforce your security policy, but many never set up the rules in it. Determining what kinds of data from what sources can go where and what data to stop cold and reject is essential. If you don’t have a security policy you really
have nothing to enforce, rendering the firewall pretty useless.
Security measures at this level are often responses to things happening that concern you. Perhaps you suspect someone is hijacking your email, so you install an email gateway. Or, one of your people clicked on a website and got their computer clobbered.
Time for a web gateway. Many software and cloud service providers are making it easy to confirm logins through
multi-factor authentication by sending a six-digit number to the user’s mobile phone that must be entered after the password. And this is the spot where the AVERAGE business finds itself, and often stops. Until something even worse happens.
PROACTIVE SECURITY
At some point, concern about escalating levels of risk drives you to take a serious look at systems and data security. You may at this point call in experts to consult with you. Based on their recommendations you may decide to improve upon what you’ve already put in place. You’re being proactive.
PREPARING FOR DISASTER
Then your attention turns to higher level measures such as intrusion detection and prevention, formalized alerting and actioning of alarms when incidents occur. This soon
leads to development of a coordinated incident response protocol that includes resolving the breach, reporting it as necessary, and determining appropriate measures to prevent recurrence.
This is also the point where many organizations take a brutally honest look at their disaster preparedness. This leads to a more defined approach to data management, backup and recovery provisions, and assessment of the real value of each data asset to
quantify risks. A different aspect of disaster preparedness is having the ability to send out mass notifications from your ShoreTel phones, Mitel Connect solutions, or any other Unified Communication Solution.
ADVANCED INTELLIGENT SECURITY
One of the possible outcomes of your increased proficiency at maintaining high security levels is that more sophisticated hackers and other bad actors may come to consider you a challenge. This is not as far-fetched as you’re probably thinking it is.
Protection now requires an even more sophisticated approach involving the identification of unusual user behaviors that may indicate a stolen password or similar exploit. Your strategy will now advance so that all of your security provisions are unified,
or at least orchestrated.
ADAPTIVE SECURITY
The most powerful security posture occurs when you engage the necessary tools and expertise to begin hunting for possible threats. It may occur at your user devices or endpoints, or it may approach your entire network and the systems running on it, but now you are literally “looking for trouble.” Your risk tolerance is low and the most valuable result is that you identify and block potential threats long before they become exploits and attacks.
DISTINGUISHING BETWEEN DATA SECURITY AND NETWORK SECURITY
When evaluating your security maturity, it’s important to distinguish between data and network security.
SECURING THE NETWORK
Your goal when securing the network is to prevent disruption. DDoS and similar attacks overwhelming the network or specific hosts cause the network to stop functioning, disrupting service to users and customers. Prevention begins with early detection and contingency planning. Consider this to be every bit as critical as Disaster Recovery and Business Continuity planning, because in every important way, it is.
SECURING THE DATA
Your goal in securing the data is actually to create the last line of defense should all else fail. If an attacker gets through your firewall, passes by your intrusion detection and prevention measures, and gets at your data, your best and most important defense is to keep that data encrypted both in transport between hosts and at rest in storage.
Encrypted data without access to the decryption key yields nothing but garbled characters to the attacker. Useless. Valueless. Encrypt your data when it is in storage and encrypt it in transport from router to router and network to network.
With constantly encrypted data, your only vulnerability is that the attacker who gets through all your network defenses may corrupt your files making them useless to you. This is where your data backup discipline pays off big time.
Remember that data replication is not enough. An attacker destroying replicated volumes may not be discovered quickly enough to prevent the destroyed data from replicating to all backups. You must also frequently duplicate all data to a safe location offsite and unknown to those who would attack you.
From the earliest days of data backup, they talked about “belt-and-suspenders” backup, and it’s a good metaphor today. If replication is your backup belt, duplication is your backup suspenders. Be sure both are in place, constantly updated, and strictly monitored.
DOES REGULATORY COMPLIANCE GUARANTEE SECURITY?
In a word, no.
It is possible to be fully compliant with government regulations but still be insecure, and it is just as easily possible to be highly secure but not fully compliant. Why?
While most regulatory acts regarding data include security-related requirements, they are in no way meant to be comprehensive, do not necessarily include security requirements at every level of the ISO-OSI model, and were never designed nor intended to prescribe a comprehensive data and network security strategy.
One of the strengths of governmental regulation that serves security experts well is their requirement that you not only implement safeguards, but that you can also demonstrate and
document their effectiveness. This instills a discipline that double and triple checks each and every security measure at each level of the network.
HIPAA, as an example, is the Health Insurance Portability and Accountability Act, meaning that it requires healthcare professionals and their business associates to all accept accountability for assuring patient privacy when transporting protected health information (PHI) from one entity to another, whether electronically or in printed form. HIPAA compliance requires not only digital protections, but policy and procedural adherence as well, and all of it must be documented.
In ways like this, many regulatory acts go far beyond the ISO-OSI model to levels that were not included by the ISO, but probably should be.
So, what do you think your Security Maturity level currently is? Where do you want it to be?
You can research some of the security solutions we offer or contact us to discuss your situation.


